Over the past year, the ecommerce sector has seen a surge in sales. Owing to the pandemic, ecommerce platforms have embraced the digital journey of millions of consumers to drive growth, revenue, and customer engagement. According to a report by UNCTAD, online sales surpassed brick and mortar sales and continue to grow year on year.
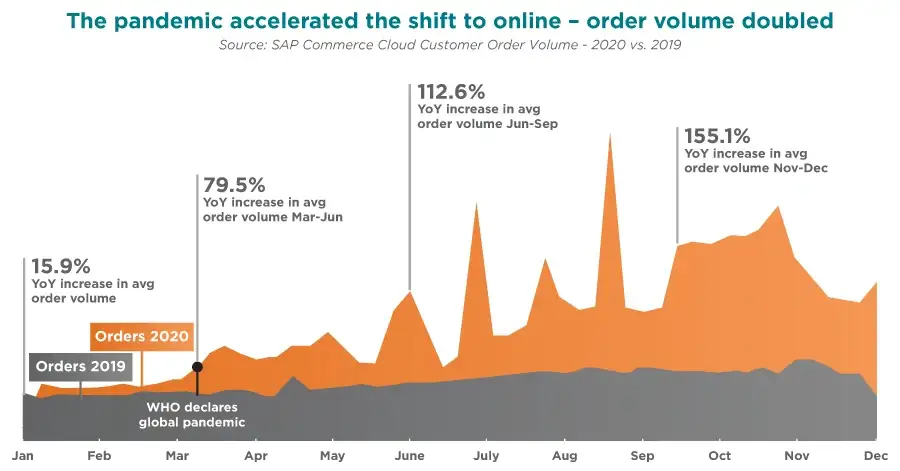
But as digital sales increase, the landscape has attracted the attention of several threat actors. The retail sector contributed the largest share of cyber incidents in 2020. From Claire’s to Warner Music Group, large ecommerce enterprises were victims of Magecart attacks. According to Webscale’s Global Ecommerce Security Report, Magecart-type attacks targeting storefronts rose by 81 percent in 2020 compared to the previous year. Other major types of attacks that stood out included credit card fraud, credit card skimming, and account takeover.

Hackers and their technology, tools, and techniques are constantly changing. But are our systems able to cope with the changing landscape?
Top 5 security trends in 2022
While ecommerce platforms have implemented innovative technologies to boost customer interactions, the security platform is a work in progress. No system is completely safe from threat, but enterprises can adopt technologies to stay ahead of the threat. The past year is a clear indication that our traditional security measures are ineffective. CISOs need to look at upcoming innovative technologies to redefine their security measures.
AI/ML-led automation
Artificial Intelligence (AI) and Machine Learning (ML) led analytics have helped the ecommerce sector better serve its customers. The same technology finds its way to automate detection and remediation in case of an attack. AI-driven solutions help develop better threat intelligence and operate efficiently to eliminate risks.
Real User Monitoring (RUM)
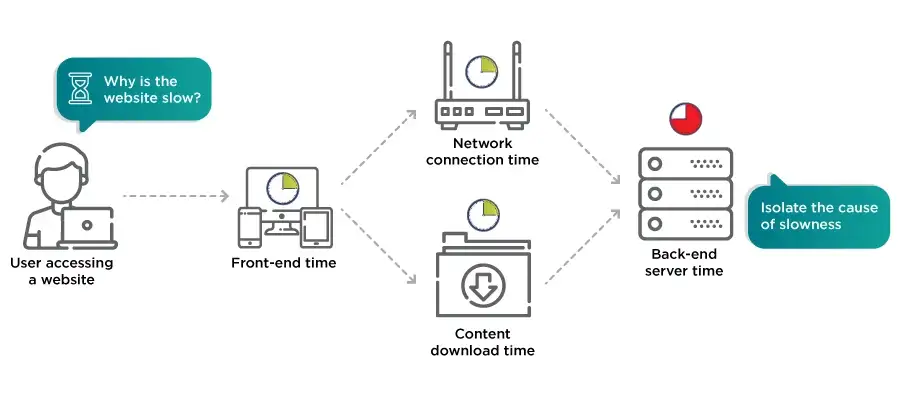
Ecommerce is a fast-moving sector with millions of users active on a platform requiring constant uptime, speed, and personalization. Organizations require real-time visibility into customer interactions across channels and platforms. RUM helps organizations by merging frontend and backend data to holistically monitor end-user experience, prioritize issues, and allow organizations to make decisions effectively.
Fraud detection
Ecommerce fraud takes many forms, including chargebacks, credential stuffing, and account takeover (ATO) attacks – negatively impacting ecommerce revenues. Many ecommerce platforms are looking to machine learning (ML) to create flexible systems that can learn on the go. These systems help in real-time data processing, finding hidden patterns, automating verification processes, and moving beyond legacy fraud detection solutions.
Real-time CSP protection
The rise in cloud services translates to more and more involvement of third-party providers. The lack of visibility into third-party applications increases Magecart and digital skimming attacks, resulting in the loss of critical consumer data. The vulnerabilities in such systems can be approached with real-time content security policy (CSP). The goal of CSP is to defend against the injection of malicious code with clear-defined page permissions. CSP effectively protects web applications against client-side vulnerabilities. However, the complexity and cost of maintenance of CSP continue to be a strong deterrent for its widespread adoption.
Security at the edge
As the digital world continues to expand, cloud adoption is on the rise to accommodate new users, technologies, products, and services. Security is no longer limited to perimeter fencing at the front-end. Modern security requires a perimeter-less solution that provides a 360-degree view of the customer. Edge computing is an extra layer of security that helps mitigate attacks across an expanding threat surface. It’s zero-trust security model is designed for the agile, fast, and ‘always on’ consumer base, replacing the traditional ecommerce security measures. Its distributed network architecture also helps in preventing a complete business shutdown in case of a breach. Business leaders have the option to disconnect only the affected node – before it spreads across the network ecosystem.
What you should do next
Businesses must stay ahead of threats to succeed. But, staying ahead of the threat requires a change in how we approach security. The first step is in adopting a security-first approach.
By implementing advanced monitoring and security at every stage of the customer journey, organizations can move from a reactive to proactive security approach. The inside-out perspective of data security would help organizations to monitor everything, automate breach detection, fix breaches quickly, and reduce breach impact.
Webscale’s cloud platform for modern commerce is designed and built with a security-first approach. Our 360-degree security solution provides ecommerce organizations with robust, always-on security to allow early detection and mitigation of risks.
If you’d like a complimentary audit of your site’s security, or just some guidance, email us at security@webscale.com and I’ll connect you to one of our security specialists.







