Last Updated On: August 3, 2021
UPDATE: 2021 is a new year, but it’s the same story – Paypal has sent new communications to merchants on Magento 1 (M1) warning them that they will no longer be PCI compliant if they, like thousands of others, remain on the platform. The response to this also hasn’t changed. PCI compliance requires M1 storefronts to be signed up with an official vendor supplying security patches. Failure to show this during your next PCI audit, and you could lose the ability to process credit cards. Webscale has continued to regularly release patches for both M1 Community and Enterprise (now Open Source and Commerce) – 49 to date – and we will continue to do so for the foreseeable future. Despite the email Paypal sent out again, you can stay safe, and compliant on M1, while you plan your next move, on your timeline. Read our latest blog on the topic here.
We likely all saw the emails. Social media was all over it. Merchants staying on Magento 1 (M1) likely gulped and muttered something perhaps not suitable for a corporate blog.
What am I talking about? The “Acquirer Advisory” from Visa and now PayPal, who joined the same FUD battle last week, demanding “urgent action” from any M1 merchant planning to stay on the platform past its planned end of life (EOL) in June 2020.
The reports and emails from both companies stated much of the same information, that merchants failing to migrate to M2 by the cut off date would “be vulnerable to security breaches and pose an increased risk to the security of payment card data.” They also said that “failing to migrate a Magento 1 ecommerce website will cause merchants to fall out of PCI DSS compliance because no security patch will be available for new vulnerabilities after June 2020.”
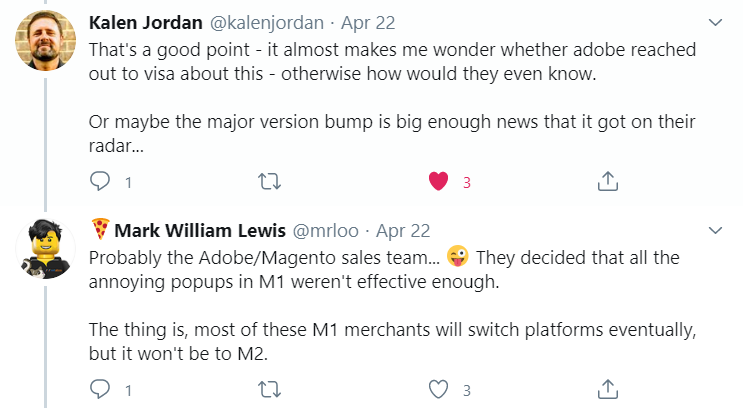
Now, how the end of life of an old ecommerce application popped up on the radar of credit card and payment provider behemoths Visa and PayPal, and why it concerned them so much that they felt the need to put out these advisories is a question for the ages. At least as far as Visa was concerned, the Twittersphere was on the right track in this author’s opinion.
As for PayPal…well, the fact that they are partnering with Magento to offer loans to merchants to migrate to M2, and considering that no other hosting providers are able to participate in the program, should provide you with enough reasons for their sudden need to jump into the fray.
What is important for everyone out there to understand is that there are lots of EOL versions of ecommerce applications out there that are fully PCI compliant. Magento 2.0, 2.1 and 2.2 are all EOL, and there are many variants of WooCommerce still in use that fall into the same category.
Just because a platform is EOL, or never had the support of a large public company, does not mean it automatically falls out of compliance. Note what the Visa document said for example: “failing to migrate a Magento 1 ecommerce website will cause merchants to fall out of PCI DSS compliance because no security patch will be available.”
But…there will be patches available.
For our Webscale M1 Support platform, we commit to virtually patch M1 applications as soon as vulnerabilities are discovered, and we’ll be working with our partners to release formal patches, quicker and more frequently than Magento were themselves.
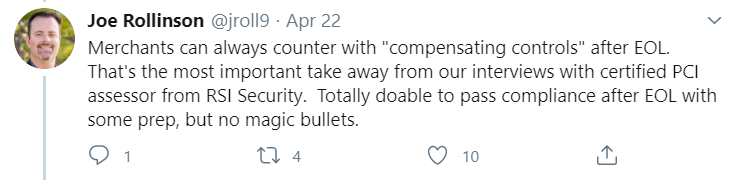
But patches aside, the bottom line is that if you don’t maintain your storefront, it will absolutely fall out of compliance. What does “maintain” mean in this case? Put simply, it means having the right compensating controls in place to satisfy the PCI council. Here is what they say about them specifically (page 24):
“Compensating controls may be considered for most PCI DSS requirements when an entity cannot meet a requirement explicitly as stated, due to legitimate technical or documented business constraints, but has sufficiently mitigated the risk associated with the requirement through implementation of compensating controls.”
We recently did a livestream on this topic, with certified PCI assessors, RSI Security, and Best Worlds, a top agency in the Magento ecosystem. During that session we went into details on these controls and how, if implemented correctly, they can keep your storefront compliant until you are ready to either re-platform to a supported version of Magento 2, or migrate to another platform.
Best Worlds did a really nice job explaining these controls, in detail, on their blog, but for those afflicted with the same short term attention span as me, here is a quick summary of those controls:
Added Web Security
This is where we, Webscale, can really help as our M1 Support platform has everything you need, from a Web Application Firewall (WAF), to a robust set of Content Security Policies (CSP) to prevent unauthorized scripts from executing on your site. Patching plays a big role here, so you need to ensure you have a provider for those, and as I mentioned previously, we have you fully covered there as well.
Added Scanning
Increase the frequency of your vulnerability scanning to monthly, or even more frequently. This will communicate to the PCI council that you are going above and beyond which, given the fact you are on an EOL platform, will help considerably. Webscale has you covered here too.
Added Monitoring
At Webscale, we call this intrusion detection, and it’s critical. Credit card skimming is at the top of hacker’s to-do list when they get access to your site. Only by monitoring all file changes, and checking that they are consistent with internal development work only, can you ensure that no one has accessed your site without your knowledge. If someone has, you need a plan.
Added Planning
A PCI assessor will want to see that you have considered every single eventuality, and set out a clear plan in the unlikely event of a hacker gaining access to your back end infrastructure. Think through every stage of the process, who is responsible for each piece, when the required operations (monitoring, scanning etc.) will be done and what action will be taken if required. Document it, and be ready to “show your work” (a phrase I am becoming increasingly used to hearing now I am home schooling like everyone else)
Best Worlds also prepared a nifty checklist to help you work through the right steps to stay compliant and protected.
So that’s it. Visa’s ‘advisory’ and PayPal’s message of foreboding are not the kiss of death for M1, and being on any EOL platform does not automatically push you out of compliance. It’s simply not true. You can stay on M1 as long as you are smart about going that extra few yards to demonstrate to the PCI Council that you take your customers’ security seriously, and that you have put every possible measure in place to secure your storefront.
PayPal have even backpedaled on their position since their original statements, providing links to 3rd party resources to help merchants, staying on M1, stay compliant. Other payment providers, like Stripe, are doing the same, ensuring there is no confusion about their ongoing support for M1 merchants that have taken appropriate action to secure their storefronts.
There are plenty of open source platforms in the world that are secure enough to warrant PCI compliance. Like M1, they have a community around them that builds these patches. We are that community for M1, along with a several other companies supporting the initiative.
Webscale and its partners can get you to where you need to be with M1, so if you’re up that specific creek, and you’re looking for a paddle, drop me an line at ah@webscale.com and I’ll share more info about the Webscale M1 Support platform.







